Top 10 Examples of White Collar Crime
A crime will always be a crime irrespective of the amount of damage it causes and who commits it, a high-ranking political/corp...
A crime will always be a crime irrespective of the amount of damage it causes and who commits it, a high-ranking political/corporate official or a poor individual. However, the name of the crime is indeed a matter of who the perpetrator is.
People from lower social class, who carry out a violent or non-violent crime like bank robbery, are generally known as blue-collar criminals. And when white-collar professionals commit a crime that is mostly non-violent in nature, it is called a white-collar crime. The major motivation of these white-collar or government and business professionals is financial gain.
In 1939, the sociologist Edwin Sutherland was the first to define ‘white-collar crime’ in criminology. He defined it as "a crime committed by a person of respectability and high social status in the course of his occupation."
White-collar crime examples typically include cybercrime, money laundering, bribery, Ponzi schemes, labor racketeering, embezzlement, forgery, copyright infringement, identity theft, and insider trading. Know here what each of them exactly means and how are they monitored or tackled.
1. Cybercrime

What is it?
Cybercrime or a computer-related crime is a crime associated with computers and networks in which crime may be done using a computer or where the computer itself is the target. In this crime, a person or nation's security and financial health are threatened.
According to Dr. Debarati Halder (Legal Scholar & MD of Centre for Cyber Victim Counselling) and Dr. K. Jaishankar (Sr. Associate Professor in the Dept. of Criminology & Criminal Justice), cybercrimes are defined as the offenses committed to advertently harm the reputation of an individual or group of individuals using modern telecom networks such as the Internet and mobile phones.
They further define 'cybercrime against women' as "Crimes targeted against women with a motive to intentionally harm the victim psychologically and physically, using modern telecommunication networks such as the internet and mobile phones".
Research by market analysts at Juniper Research suggests, (16.1)
“The global cost of cybercrime will reach $2.1 trillion by 2019, a fourfold increase from the 2015 estimate of $500 billion.”
Cybercrime comprises multiple activities including but not limited to computer fraud, cyber terrorism, cyber extortion, cyber warfare, espionage, financial theft, drug trafficking, harassment, computer virus, malware, denial-of-service attacks, and obscene/offensive content.
Combating the crime:
- Legislation: Cybercriminals exploit developing countries to evade detection and prosecution from law enforcement when laws are weak or non-existent. While it is difficult in certain cases, agencies like the FBI use deceptive stratagem to catch criminals.
In April 2015, former US President Barack Obama released an executive order to counter cybercrime. It allows the US to freeze assets and block the economic activity of convicted cyber criminals within the country. The European Union adopted directive 2013/40/EU. All offenses included under the directive, procedural institutions and other definitions are also of the Council of Europe's Convention on Cybercrime.
- Penalties: Private companies hire some white-hat (ethical) hackers as information security experts because of their deep knowledge of computer crime. Banning convicted hackers from using computers and employing nuanced approaches such as restricting individuals to specific devices that are subject to computer monitoring and/or computer searches by probation and/or parole officers. Also, penalties for cybercrimes in New York ranges from a fine to short or long-term imprisonment.
- Awareness: Technological advancements have resulted in more and more people relying on the internet. As they store confidential and sensitive information (credit card and bank details) online, its risk of stealing increases. Hence the critical information can be protected by spreading awareness about it can be done and knowing the tactics used by criminals to execute the crime.
2. Insider trading

What is it?
Insider trading is a type of trading in which a public company’s nonpublic information about securities (such as stocks or bonds) is illegally used by an insider. This insider includes the company's officers, directors, the beneficial owner of more than 10% of a class of the company's equity securities, brokers, associates, and family members.
This trading is considered unfair to other investors who don’t have access to information as the one having insider information may make much larger profits than a typical investor wouldn’t. A study says that illegal insider trading increases the cost of capital for securities issuers thereby decreasing overall economic growth.
How is it monitored?
The governing rules and extent of enforcement for insider trading vary significantly from one country to another. In order to monitor illegal trading, many jurisdictions require reporting of trading within a few business days.
The Securities and Exchange Commission monitors the trading by examining the trading volumes of a particular stock. The volumes generally go up after the material news is issued to the public. However, when no such information is provided and volumes increase greatly, it can be a warning. Then, the SEC probes into the matter to find out who’s responsible for the unusual trading and if it was illegal.
In US law, the misappropriation theory is now accepted which states that anyone misappropriating and trading information from his or her employer in any stock (either the employer's stock or the company's competitor stocks) may be guilty of insider trading.
3. Money laundering

What is it?
Money laundering is the process of concealing the source of money obtained illegally through serious crimes such as evasion of international sanctions, drug trafficking, and terrorist activity. It also includes misuse of the financial system (securities, digital currencies, credit cards, and traditional currency) and is conflated with other forms of financial and business crimes.
It involves three steps namely placement, layering, and integration. Placement is the act of bringing dirty money (money obtained through illegal and criminal methods) into the financial system. Layering is the act of hiding a source of money through a series of complex transactions and bookkeeping exercises. Integration is the act of procuring that money through allegedly legitimate means.
How is it combated?
Anti-money laundering (AML) involving legal controls that require financial institutions and other regulated entities to prevent, detect, and report money laundering activities. It became globally prominent with the formation of the Financial Action Task Force (FATF) and the announcement of an international framework of AML standards.
An effective AML necessitates jurisdiction to illegalize money laundering, rendering authorities the power & tools to investigate, report suspicious activities, establish risk-based controls, and perform other related activities.
- Criminalization: The elements of the crime are stated in the United Nations Convention Against Illicit Traffic in Narcotic Drugs and Psychotropic Substances and Convention against Transnational Organized Crime.
- Role of financial institutions: Most of the financial institutions and non-financial institutions present globally are required to identify and report suspicious transactions to the financial intelligence unit in the respective country.
Also, anti-money laundering software is used for filtering customer data and classifying it according to the level of suspicion so as to inspect it for anomalies (a sudden and substantial increase in funds, a large withdrawal, or moving money to a bank secrecy jurisdiction). Smaller transactions meeting certain criteria can also be flagged as suspicious.
- Enforcement costs & associated privacy concerns: The financial services industry has been expressing concerns regarding the increased costs of anti-money laundering regulation and the limited benefits that it has. Apart from the economic costs related to the implementation of anti-money-laundering laws, an improper attention to data-protection practices may involve unreasonably high costs to individual privacy rights.
Many countries are obligated by several international instruments and standards for the enactment and enforcement of money laundering laws so as to stop narcotics trafficking, international organized crime and corruption.
- Role of global organizations: The intergovernmental body FATF develops and promotes an international response to tackle money laundering. It unites legal, financial and law enforcement experts to achieve national legislation and regulatory AML and CFT reforms.
The United Nations Office on Drugs and Crime has a website imolin.org (International Money Laundering Information Network) that provides comprehensive information and software for anti-money laundering data collection and analysis. (16.2)
4. Forgery

What is it?
Forgery is a process of creating, altering, or emulating objects, documents, or statistics for a deceitful purpose such as earning profit by selling the forged item. Studio replicas & reproductions, copies aren’t forgeries but they can become so through knowing and willful misrepresentations.
Counterfeiting is the forging of money or currency. However, consumer goods can also be counterfeits if the designated manufacturer or producer given on the label or flagged by the trademark symbol does not manufacture or produce them. A forged document or record is often called a false document.
Criminal law:
Forgery is considered an offense in different sections of criminal acts prevailing in different countries. A person found guilty of forgery may be liable to fine, imprisonment, or both on conviction or indictment.
5. Embezzlement

What is it?
Embezzlement, also known as peculation, is the misappropriation of assets (funds or property) by an individual to whom it was entrusted to care or management. It is a type of financial fraud. It is generally a pre-planned crime in which an embezzler takes precautions to hide his/her activities as the crime is taking place without the knowledge or consent of the asset owner.
Embezzlement usually occurs in a small ratio or fraction of the total funds that the embezzler manages so as to minimize its risk of detection. When the embezzler succeeds, embezzlements continue for years (or even decades) without any investigation. It is only investigated when a large proportion of funds are needed at a time or when a major institutional reorganization occurs requiring the complete and independent accounting of all real and liquid assets. It’s then that the victim realizes his/her funds, savings, assets or other resources have gone missing and that he/she has been duped by the embezzler.
In the US, embezzlement is a statutory offense that, depending on the circumstance, maybe a crime under state law, federal law, or both. Thus, the definition of the crime of embezzlement varies according to the given statute. The typical criminal elements of embezzlement are: (i) the fraudulent (ii) conversion (iii) of the property (iv) of another person (v) by the person who has lawful possession of the property.
Safeguards against the crime:
A common defense against embezzlement is regulating the internal controls such as separation of duties. Yet another method to prevent embezzlement is to frequently and unexpectedly transfer funds from one entrusted person to another when the funds are needed for withdrawal or use. This ensures that the complete amount of the funds is available and no fraction of the savings has been embezzled.
6. Ponzi schemes
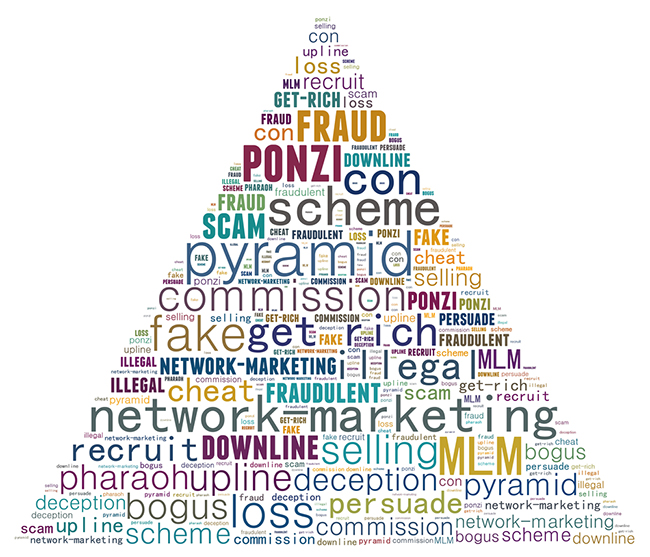
What is it?
Named after swindler & con artist Charles Ponzi, a Ponzi scheme (or Ponzi game) is a fraudulent investment operation wherein the operator or individual pays its initial investors from the funds that he raises from later investors rather than the profit earned through legal sources.
The operators of this scheme most often attract investors by offering short-term and higher returns than other investments. No matter what the initial situation, the continuation of high returns and scheme requires an ever-increasing flow of money from new investors.
In 1920, Charles Ponzi became infamous for using the technique. His original scheme was based on the arbitrage of international reply coupons for postage stamps. He diverted the money of later investors to make payments to himself and his initial investors.
Unraveling of a Ponzi scheme:
When the scheme isn’t stopped by authorities, it collapses due to one of the following reasons:
- When the promoter disappears by taking away all the remaining investment money.
- As the scheme requires continuous investments for funding higher returns, so once the investment gets slowed down and the scheme collapses since the promoter faces problems in paying the promised returns. This liquidity crisis causes panic since more and more people begin asking for their money.
- External market forces like a sharp slump in the economy lead to investors withdrawing their funds (partially or wholly).
7. Identity theft

What is it?
Identity theft is intentionally using or stealing someone else’s identity for financial gain, obtaining credit or other benefits in the other person's name causing disadvantage or loss to that person. This white-collar crime occurs when a person uses another person’s personally identifying information such as their name, identifying number, or credit card number without his/her permission to carry out fraud or other crimes.
A non-profit named Identity Theft Resource Center splits identity theft into the following five categories: (16.3)
- Criminal identity theft (impersonating as another person when seized for a crime)
- Financial identity theft (using someone else's identity to get credit, goods, and services)
- Identity cloning (using someone else's information to put on his/her identity in daily life)
- Medical identity theft (using someone else's identity to get medical care or drugs)
- Child identity theft (using a minor's identity for personal gain)
This crime is used to enable or fund other crimes such as illegal immigration, terrorism, phishing, and espionage. A lot of cases for identity cloning are reported in which payment systems including online credit card processing and medical insurance are attacked.
Identity protection:
- Individual identity protection: It can be partially controlled by NOT identifying oneself needlessly(a form of information security control known as risk avoidance). This means that organizations and IT systems & procedures shouldn’t seek too much personal information or credentials for identification and authentication.
Storing and processing of personal identifiers (such as Social Security number, national identification number, driver's license number, credit card number, etc.) increases identity theft risk unless it is properly secured. It is better to commit personal identifiers to memory and rather use mnemonic techniques or memory aids. It thus reduces the risks of stealing these records.
Also, commercial identity theft protection/insurance services have also become available in several countries in recent years. These services purport to help protect the individual from identity theft or help detect that identity theft has occurred in exchange for a monthly or annual membership fee or premium.
- Identity protection by organizations: Biometric information systems such as fingerprints, for identification and authentication, are said to help in preventing identity theft. However, these methods also have certain technological limitations and associated privacy concerns.
8. Copyright Infringement
What is it?
Copyright infringement involves a violation of rights protected under copyright law. It is making use of copyrighted works without the permission of the copyright holder and infringing certain exclusive rights (right to reproduce, distribute, display or perform the protected work, or to make derivative works) that are granted to only him/her. The copyright holder could be the work’s creator, or a publisher, or other business to whom copyright has been assigned.
Preventive measures:
- Legal: Legislatures and several corporations have adopted preventive measures to keep a check on copyright infringement primarily on the digital platform. The strategies are education, publicizing anti-piracy litigation successes, anti-circumvention laws, international agreements, civil & criminal legislation, and imposing forms of digital media copy protection.
Apart from maintaining international copyright treaty obligations for the provision of general limitations and exceptions, countries have laid down compulsory licensing laws that apply particularly to digital works and their usage.
Some of the copyright owners reduce infringement by employing "open" licensing strategies instead of personally negotiating license terms with users who must ask for the copyright owner’s permission. The copyright owner publishes and distributes the work with a prepared license that could be used by anyone if they abide by certain conditions. GNU General Public License (GPL) and the Creative Commons licenses are free software licenses primarily applied to visual and literary works.
- Protected distribution: In order to protect films from piracy, the general procedure is releasing the movie first in theaters (theater window) and then on Blu-ray and DVD (video window) maintaining an average duration of nearly 16 and a half weeks between the two releases. In theaters, a film’s digital version is often delivered in data storage devices by couriers instead of data transmission.
The data can be encrypted, making a key being that would work only at specified times to avoid leakage between screens. Coded Anti-Piracy marks may also be added to films for identification of the source of illegal copies.
9. Bribery

What is it?
Bribery is the practice of offering something (goods, money, or another form of recompense) to an official or another person either to gain an illicit benefit or to alter the recipient’s conduct that he/she otherwise wouldn’t. According to Black's Law Dictionary, bribery is defined as “offering, giving, receiving, or soliciting of any item of value to influence the actions of an official or another person in charge of a public or legal duty.”(16.4)
Prevention:
International businesses and organizations have been implementing strong programs to control bribery. External verification of business partners and employees is essential to ensure its proper working and that it meets international standards. The international best practices used in external verification processes for ensuring the success of bribery prevention program include Council for Further Combating Bribery of Foreign Public Officials in International Business Transactions (Annex 2), ISO 26000 norm (section 6.6.3), or TI Business Principles for Countering Bribery.
The external verification is also required to assert that all that was done to thwart corruption in which bribery prevention programs serve as evidence. Proportionate procedures, top-level commitment, risk assessment, due diligence, communication, and monitoring and review are the six principles issued by the Ministry of Justice for bribery prevention.
10. Labor racketeering
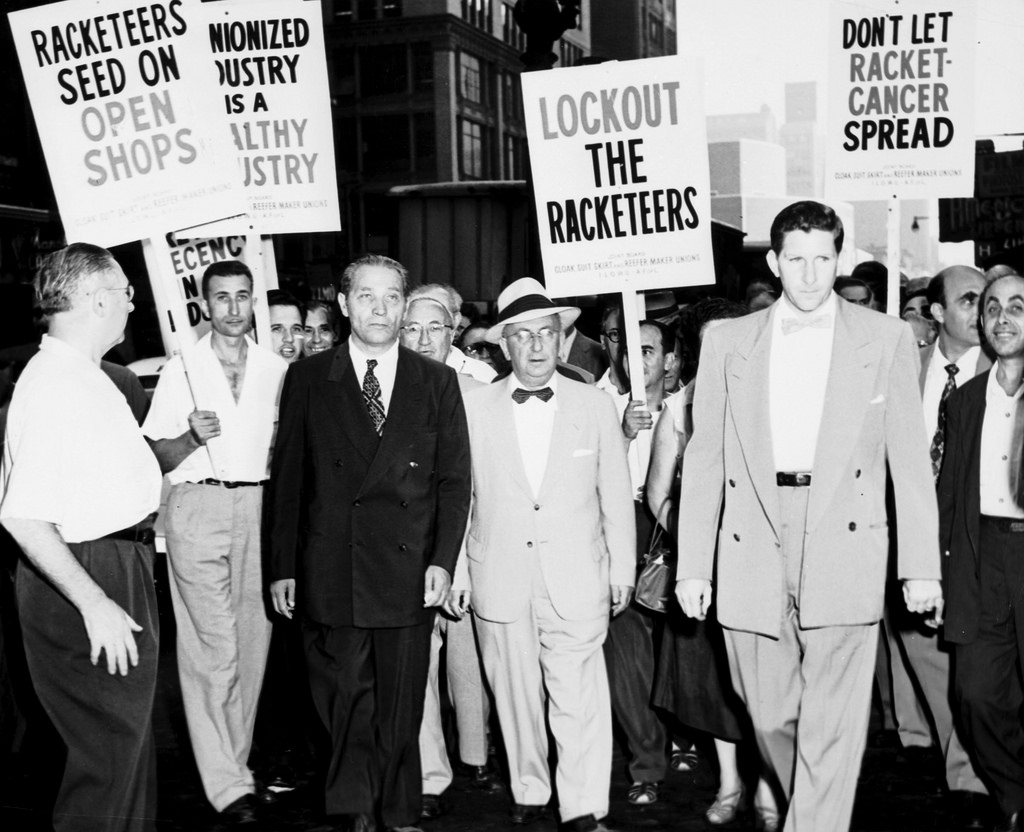
What is it?
Labor racketeering involves illegal infiltration, exploitation, and control of unions, employer entity, workforce, or employee benefit plans. It is executed through illegal, fraudulent, and violent ways for personal profits.
The organized labor is misused for criminal purposes in labor racketeering. Criminals of organized crime groups extort the labor union bosses (can also be the bosses themselves) and ask the workers to go on strike. As a result, this leads to a lot of wastage of money, time, and resources to the company/contractor as he can’t get the work done. And then, the company/contractor is forced to pay a huge amount of money so that workers go back to work and work gets started again. (16.5)
Control:
In the United States, RICO (Racketeer Influenced and Corrupt Organizations) Act allows law enforcement to charge a person or group of people with racketeering, defined as committing multiple violations of certain varieties within a ten-year period.
Popular Posts
12 Unseen Pictures of Sofia Vergara That are too Hot To Handle
An actress, comedian, producer, television host Sofia Vergara is one of the most loved personality in the TV industry. Bo...
Chandan Roy
Top 10+ McDonald's Characters That Are Better Alternative To The Creepy Clown
When you visit McDonald's, you are entertained by several McD characters designed for kids. Do you know how many Mc D characters are there in total? Let's find it out.
Aaditya M
10 Largest Organs In Human Body
Human body consists of 70 organs that are highly specialized in performing different functions. Millions of cells form part of a...
Swati Bhandari